
- KYC compliance is not just about customer verification. Businesses also need clear documentation, updated policies, SOPs, staff acknowledgment records, approval trails, and audit-ready evidence.
- Document chaos can become a compliance risk. Scattered files, outdated policy versions, email-based approvals, and missing acknowledgment records make it harder to prove compliance when regulators ask.
- Mekari Officeless DMS helps businesses stay audit-ready. With centralized documents, approval workflows, access control, templates, and document governance, teams can manage KYC documentation more securely and consistently.
Global KYC fines reached a record high of $51 million in the first half of 2024, up 102%, while total AML/KYC penalties hit $263 million in the same period (Fenergo). But most businesses do not fail audits because of bad intentions.
They fail because critical documents, from policies and SOPs to customer records, are scattered, outdated, or hard to access when regulators ask for proof.
That is why document management is no longer just an admin tool. With the right Document Management System (DMS), businesses can centralize KYC documents, control versions, track approvals, and keep audit trails ready.
In this guide, we will look at what KYC compliance requires, why messy documentation creates risk, and how Mekari Officeless DMS helps teams stay inspection-ready without last-minute scrambling.
What is KYC compliance?
KYC compliance, or Know Your Customer compliance, is the regulatory process businesses use to verify who their customers are, by assessing risk and monitoring customer activity to prevent fraud, money laundering, and other financial crimes.
It is built on three main pillars:
- Customer Identification Program (CIP): Collecting and verifying customer details, such as name, ID, address, and date of birth.
- Customer Due Diligence (CDD): Assessing customer risk, beneficial ownership, and the purpose of the business relationship.
- Enhanced Due Diligence (EDD): Applying deeper checks for high-risk customers, politically exposed persons (PEPs), and large or unusual transactions.
KYC is part of a broader Anti-Money Laundering (AML) framework, guided by international standards such as FATF and national regulations such as OJK rules in Indonesia.
Today, it applies not only to banks, but also to fintechs, insurers, crypto platforms, real estate businesses, and professional services firms.
Why KYC compliance is getting harder to maintain and costlier to fail
KYC compliance is becoming more difficult because businesses now face pressure from three directions at once: rising penalties, higher operational costs, and wider regulatory obligations. This makes manual, scattered document management increasingly risky.
Financial penalties are surging
Regulators are becoming more aggressive in enforcing AML and KYC requirements. Businesses that fail to maintain proper documentation, customer checks, and audit trails can face serious financial consequences.
- KYC fines increased by 102% to a record $51 million in H1 2024, according to Fenergo.
- Total global AML/KYC enforcement actions surged 31% in H1 2024, reaching $263 million.
- In 2024, penalties against banks globally rose 522% to $3.65 billion, based on Fenergo’s annual report.
- Non-compliance costs organizations an average of $14.82 million annually, almost three times higher than the average cost of maintaining compliance programs at $5.47 million, according to Ponemon Institute.
KYC is operationally expensive and getting worse
KYC is not only costly when businesses fail. It is also expensive to manage day to day, especially when teams still rely on manual reviews, disconnected systems, and slow document collection.
- The average cost of a single KYC review has risen 17% since 2022, now averaging $2,211 per review.
- 70% of firms lost clients due to inefficient or slow onboarding processes, according to Fenergo’s 2025 Financial Crime Industry Trends Report.
- 52% of financial institutions employ between 1,500 and 2,500 full-time staff for KYC operations.
Regulatory scope is expanding
KYC obligations are no longer limited to banks. Regulators are extending AML/KYC expectations to more industries as financial crime risks spread across digital platforms and professional services.
- 82% of global organizations cite data privacy and security as their top compliance challenge. (HyperVerge)
- Australia’s 2024 AML reform bill expanded KYC obligations to legal professionals, accountants, and real estate agents, signaling a broader trend that may extend across other APAC markets.
- Asia-Pacific firms saw the largest single-year increase in KYC penalties, with a 266% surge in H1 2024 compared with H1 2023.
As penalties rise and regulatory coverage expands, businesses need a reliable way to manage policies, customer records, version history, approvals, training evidence, and audit trails before regulators ask for them.
What KYC compliance actually requires: A documentation perspective
KYC compliance is not only about verifying customer identity. From a documentation perspective, it also requires businesses to maintain clear, updated, and accessible records that prove every KYC process was performed correctly.
The required documents usually include:
- Identity verification documents: Government-issued IDs, passports, tax ID numbers, proof of address, and other documents used to confirm customer identity.
- Risk assessment records: Customer risk scores, risk categorization records, and the methodology used to classify customers as low, medium, or high risk.
- Compliance policies: Internal AML/KYC policies, board-approved documents, approval dates, and version history showing when each policy was updated.
- SOPs: Step-by-step procedures for customer due diligence, escalation processes, document checklist requirements, and review workflows.
- Staff acknowledgment records: Proof that employees have read, understood, and acknowledged the latest policies, especially after updates or regulatory changes.
- Audit trail records: Logs showing who accessed, edited, approved, or processed compliance documents, along with the date and time of each action.
- Ongoing monitoring records: Periodic customer review notes, red flag investigation records, and Suspicious Activity Report (SAR) documentation.
The key principle is simple: regulators do not only ask, “Do you have policies?” They ask, “Can you prove your staff followed them?”
This is where many organizations face a documentation gap. A company may have strong KYC policies written somewhere, but if employees use outdated versions, store records across emails, or cannot prove policy acknowledgment, the risk exposure remains high.
In the eyes of regulators, undocumented compliance can look the same as non-compliance.
The hidden root cause of KYC compliance failures: Document chaos
Most KYC compliance failures do not happen because a company intends to ignore regulations. More often, they happen because the organization’s document infrastructure is broken.
Policies exist, but staff cannot find the latest version. SOPs are updated, but no one can prove who received or acknowledged them. Customer records are stored across email threads, shared drives, WhatsApp messages, or physical folders. When regulators ask for evidence, teams end up scrambling to reconstruct the compliance trail manually.
This document chaos usually appears in several ways:
- Outdated policy versions in circulation: Staff may still use SOPs, risk assessment forms, or customer identification checklists that were replaced months ago, simply because there is no reliable way to distribute updated versions and confirm receipt.
- No proof of staff education: Regulators increasingly expect evidence that employees have received compliance training and acknowledged updated policies. Without a tracking system, companies cannot prove what staff knew, when they knew it, or whether they followed the latest procedure.
- Scattered document storage: Critical KYC documents may be spread across inboxes, shared folders, messaging apps, and printed files. During an audit, retrieving the right record can take days instead of minutes.
- No version control: Multiple “final” versions of the same policy can exist at the same time, with no clear record of which one is valid or who made the latest change.
- Approval workflows done via email: Policy reviews, SOP updates, and compliance approvals are often handled through email chains. This makes it difficult to show a clean, timestamped approval trail when regulators ask for it.
The problem is not just administrative inefficiency. In KYC compliance, poor document control can quickly become regulatory risk.
| Document risk scenario | Manual or scattered process | Centralized DMS |
|---|---|---|
| Policy distribution | Emailed to staff; delivery unconfirmed | Published to all staff; acknowledgment tracked |
| Version control | Multiple versions in circulation | Single source of truth; outdated versions archived |
| Staff education proof | No formal record | Read and acknowledgment log per user |
| Audit retrieval time | Days of manual searching | Minutes via search and filter |
| Document approval trail | Email chains and informal follow-ups | Timestamped, role-based approval workflow |
How KYC compliance software works
KYC compliance software refers to tools that help organizations manage the full compliance lifecycle, from verifying customer identity and onboarding new clients to monitoring risk and preparing audit documentation.
In practice, KYC compliance software usually covers two key areas:
Customer-facing KYC tools
These tools focus on verifying customers and assessing their risk before and during the business relationship. Common features include:
- Digital identity verification or eKYC: Verifies customer identities using digital documents, biometric checks, facial matching, and document OCR.
- Risk scoring and tiering: Categorizes customers into low, medium, or high-risk groups based on identity data, transaction behavior, location, business type, and other risk indicators.
- Watchlist and sanctions screening: Checks customers against sanctions lists, politically exposed person (PEP) databases, and other risk databases.
Internal compliance document management
This is the documentation layer that supports the organization’s internal compliance operations. It helps ensure that policies, procedures, and records are controlled, updated, and easy to prove during audits. Key features include:
- Centralized policy repository: Stores AML/KYC policies, SOPs, checklists, and regulatory documents in one controlled location.
- Version control: Ensures staff always access the latest approved document while older versions are archived.
- SOP and policy acknowledgment tracking: Records which staff members have read and acknowledged updated compliance documents.
- Approval workflows: Routes policy updates, SOP revisions, and document reviews through structured approval steps.
- Audit trail logging: Tracks who accessed, edited, approved, or shared a document, and when.
- Role-based access: Limits sensitive compliance materials to authorized users based on role, department, or responsibility.
Many KYC compliance failures happen because companies focus heavily on the customer-facing layer but neglect the internal documentation layer.
They may be able to verify customers, but still fail to prove that their own staff were trained, informed, and following the right procedures at the time of an audit.
How a document management system strengthens KYC compliance
KYC compliance is ultimately a documentation discipline. Regulators do not only want to see that policies exist. They want proof that the organization follows them consistently. A Document Management System, or DMS, provides the infrastructure to make that proof easier to maintain.
A DMS strengthens KYC compliance by helping businesses:
- Keep policies current and consistently distributed: When a KYC policy is updated due to regulatory changes, OJK guidance, or internal review, the latest version can be distributed to all relevant staff while outdated versions are archived.
- Turn policy acknowledgment into evidence: A DMS records when employees open, read, and acknowledge compliance documents, creating proof that staff were informed about current KYC procedures.
- Create an unbroken audit trail: Every document action can be logged, including who created, edited, approved, accessed, or updated a file.
- Prevent document chaos at scale: Compliance documents can be stored in one centralized, searchable system instead of being scattered across emails, folders, messaging apps, or physical files.
- Support multi-role compliance governance: Compliance Officers, Branch Managers, Relationship Managers, and Internal Audit teams can each receive access based on their roles and responsibilities.
- Strengthen compliance risk control: Better document control reduces the risk of outdated SOPs, missing records, undocumented approvals, and unverified staff acknowledgment.
How Mekari Officeless DMS supports your KYC compliance infrastructure
KYC compliance depends on controlled, accessible, and audit-ready documentation. Mekari Officeless DMS helps organizations manage KYC policies, SOPs, verification procedures, and internal guidelines in one prebuilt enterprise document management system, without building custom software from scratch.
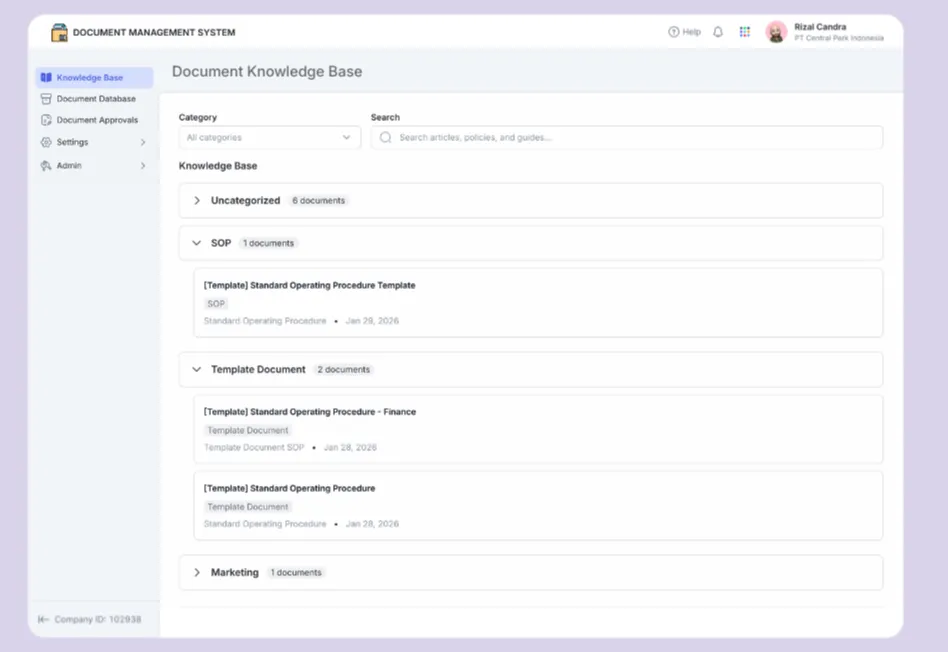
With Mekari Officeless DMS, your team can:
- Centralize compliance documents: Store approved policies, SOPs, guidelines, and procedures in one searchable digital library.
- Use document templates: Create and manage standardized documents to keep compliance records consistent.
- Automate approvals: Route new documents, revisions, and reviews through structured approval workflows.
- Control document standards: Use document types and automatic numbering to improve traceability.
- Secure access: Limit sensitive documents based on roles, groups, or positions.
- Manage governance: Configure categories, folder structures, approval rules, and document locations from one admin center.
For KYC compliance, this makes Mekari Officeless DMS more than a storage tool. It helps teams keep documents organized, approved, protected, and ready when auditors or regulators ask.
Ready to make your compliance documents audit-ready? Explore Mekari Officeless DMS.
References and methodology
Methodology
Methodology
Articles published by Mekari are developed using trusted sources, including official data, company reports, academic research, and insights from industry practitioners. Whenever possible, we refer directly to primary sources before drawing conclusions. Our editorial team reviews and verifies the information to ensure accuracy and relevance. All references are listed so readers can trace each piece of information back to its original source.
Our editorial standards
Our editorial standards
- Primary source first: We consult official product documentation and pricing pages directly, not secondhand summaries or aggregator sites.
- Fact-checking: All product features, pricing, and claims are cross-verified against each platform’s official website at the time of writing.
- No paid placement: Tools are selected based on relevance and fit for Indonesian businesses, not commercial arrangements. Mekari Officeless is included as a first-party product and is transparently labeled as such.
- Regular review: Articles are periodically updated to reflect product changes or shifts in market relevance.
References
References
Hyperverge. ‘’Global KYC Regulations in 2025: Current Laws And How To Comply’’
Fenergo. ‘’Fenergo Study: Regulatory Penalties in North America Account for 95% of Global Financial Penalties in 2024’’
